Cve score
Official websites use. Share sensitive information only on official, secure websites.
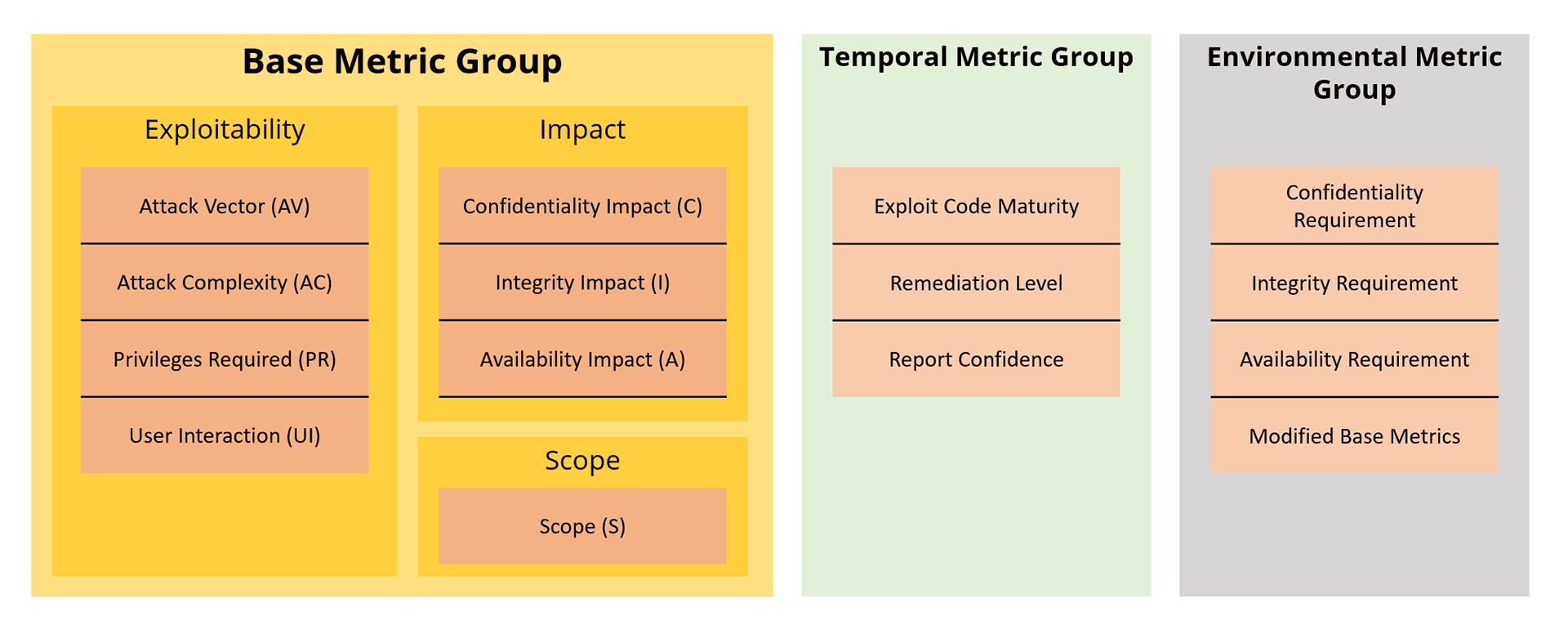
CVSS helps organizations prioritize and coordinate a joint response to security vulnerabilities by communicating the base, temporal and environmental properties of a vulnerability. Vulnerable Software. Vendors Products Version Search. Vulnerability Intel. Attack Surface. These metric groups are described as follows: Base : represents the intrinsic and fundamental characteristics of a vulnerability that are constant over time and user environments.
Cve score
See NinjaOne in action! As we move into the new year, organizations can expect the number of cyberattacks to increase significantly. In order to battle these upcoming threats, effective patching and patch management processes will be essential. This glossary organizes these security weaknesses with identification numbers, dates, and descriptions. CVSS scores quantify the severity of vulnerabilities. An IT team can use this information to determine which vulnerabilities pose the most serious threats and resolve them first before moving on to more minor weaknesses. For example, a vulnerability with a CVSS score of 8 is more of a threat than a vulnerability with a score of 3. In this case, an IT team can resolve the vulnerability scored 8 first before resolving the less serious vulnerability scored 3. The CVE provides descriptions, dates, and other information about vulnerabilities. Additionally, the CVE sometimes lists the fixes or solutions for a specific vulnerability. This valuable information allows an IT team to learn more about a vulnerability so that they can come up with a solution. These assessments help an IT team to plan, prepare, and resolve vulnerabilities before they become serious issues for an organization. They allow IT teams to categorize, prioritize, and create order when dealing with pesky vulnerabilities. With that being said, they do have certain limitations as shown below:. For example, vulnerabilities scored 7.
Although the CVE does provide some information about a vulnerability, cve score, it does not provide enough for an IT security team to use to fix the issue.
Advisories, exploits, RSS feeds and various other vulnerability intelligence features have been added along with APIs, email alerts, feeds and more. We want to save our users from Googling for information! We want to make our users more efficient and productive by providing them with easy access to information and the necessary utilities. We want to become your one-stop shop for anything related to vulnerabilities. Instead of using 20 different tools and 50 web sites, you should only need CVEdetails. Feel free to reach us at admin cvedetails. To secure your house, you first need to know how many windows and doors you have attack surface , if your doors and windows are secured properly and if they can be opened due to some defects in your locks or similar vulnerability intelligence.
Official websites use. Share sensitive information only on official, secure websites. CVSS is not a measure of risk. The Base metrics produce a score ranging from 0 to 10, which can then be modified by scoring the Temporal and Environmental metrics. A CVSS score is also represented as a vector string, a compressed textual representation of the values used to derive the score. Thus, CVSS is well suited as a standard measurement system for industries, organizations, and governments that need accurate and consistent vulnerability severity scores. Two common uses of CVSS are calculating the severity of vulnerabilities discovered on one's systems and as a factor in prioritization of vulnerability remediation activities.
Cve score
CVE is a glossary that classifies vulnerabilities. A CVE score is often used for prioritizing the security of vulnerabilities. The CVE glossary is a project dedicated to tracking and cataloging vulnerabilities in consumer software and hardware. SCAP evaluates vulnerability information and assigns each vulnerability a unique identifier. The CVE glossary was created as a baseline of communication and source of dialogue for the security and tech industries. CVE identifiers serve to standardize vulnerability information and unify communication amongst security professionals. Security advisories, vulnerability databases, and bug trackers all employ this standard.
Best yoga classes
A Bayesian Analysis". Retrieved March 2, App Security In the Base vector, the new metrics User Interaction UI and Privileges Required PR were added to help distinguish vulnerabilities that required user interaction or user or administrator privileges to be exploited. Next Steps. For more resources refer to this post on Reddit. Omits necessary context Since a CVSS score is simply a number, it does not provide any context or additional information about a vulnerability. National Institute of Standards and Technology. The attacker must have access to the broadcast or collision domain of the vulnerable system e. Instead of using 20 different tools and 50 web sites, you should only need CVEdetails. The numerical formulas were updated to incorporate the new metrics while retaining the existing scoring range of
The Common Vulnerability Scoring System CVSS is a free and open industry standard for assessing the severity of computer system security vulnerabilities. CVSS attempts to assign severity scores to vulnerabilities, allowing responders to prioritize responses and resources according to threat.
Thank you! This metric now describes how repeatable exploit of this vulnerability may be; AC is High if the attacker requires perfect timing or other circumstances other than user interaction, which is also a separate metric which may not be easily duplicated on future attempts. This value would depend on what information the attacker is able to access if a vulnerable system is exploited. These types of vulnerabilities are often described as remotely exploitable e. To address some of these criticisms, development of CVSS version 3 was started in It provides information on vulnerability management, incident response, and threat intelligence. This score is within the range 7. The availability A metric describes the impact on the availability of the target system. Vendors Products Version Search. CVE Vulnerability

It not so.
Bad taste what that
Absolutely with you it agree. I like your idea. I suggest to take out for the general discussion.